Events
WallArm sponsors May 2026 NAC-ISSA lunch
TOPIC: Business Logic Abuse: Technology Agnostic Mapping of Attack Types OWASP's technology specific top 10 lists have provided a ton of value, but it's time for a different approach to business

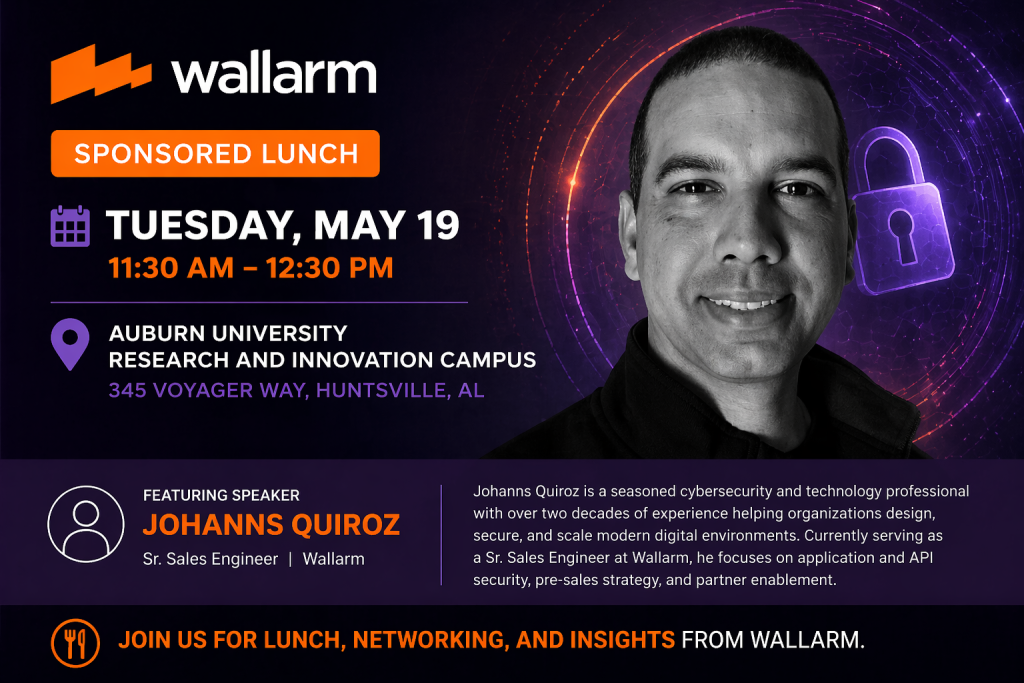
May 19 @ 11:30 am – 12:30 pm
TOPIC: Business Logic Abuse: Technology Agnostic Mapping of Attack Types
OWASP’s technology specific top 10 lists have provided a ton of value, but it’s time for a different approach to business logic abuse. The rise of APIs and complex business logic attacks requires a new taxonomy that isn’t tied to a specific technology.
Our Speaker is Johanns Quiroz. Johanns Quiroz is a seasoned cybersecurity and technology professional with over two decades of experience helping organizations design, secure, and scale modern digital environments. Currently serving as a Sr. Sales Engineer at Wallarm, Johanns supports customers across the Southeast, LATAM, and Caribbean, where he focuses on application and API security, pre-sales strategy, and partner enablement. Prior to Wallarm, he held senior technical sales and engineering roles at Horizon3.ai, where he specialized in offensive security and helping organizations proactively identify and mitigate risk. Johanns also brings deep expertise in enterprise infrastructure, having spent over 20 years as a solutions architect designing complex environments across storage, virtualization, and cloud technologies. Known for his consultative approach and ability to bridge business and technical stakeholders, Johanns is passionate about helping organizations stay ahead of evolving cyber threats while enabling innovation and growth.
