March Chapter lunch
.jpeg)
March Chapter lunch
Join us for a presentation from Sean Hopkins: Through the built-in Windows API, it is possible to establish persistence within a network on boot up and/or execution of almost any program through COM hijacking and manipulation. While many industries focus on STIG-like security measures or compliance for security, abusing flaws in Windows that will likely never be mitigated is the focus of this presentation. We will step through various methods including local and remote versions of how this exploitation works as well as techniques to hide it within a system.
Location: I3 Auditorium
Address: 655 Discovery Drive, Huntsville, AL
Start Time: 11:30AM
End Time: 12:30PM
Registration Closes On: 3/19/2019 11:30AM
upcoming events
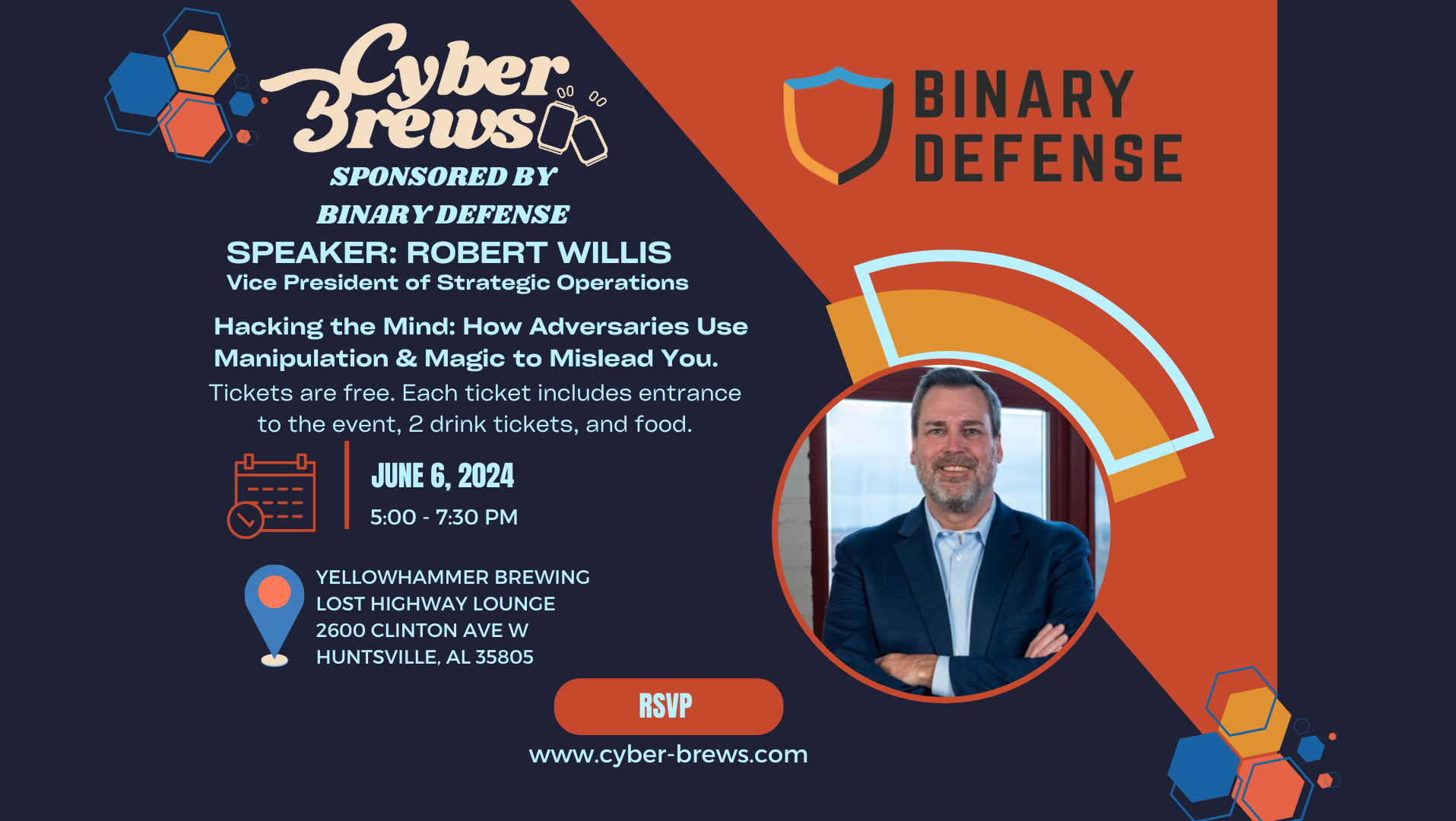
Cyber Brews Sponsored by Binary Defense
Join us for delicious brews, food, and a short presentation of Binary Defense's Managed Detection and Response capabilities.
Eac...

Gray Analytics sponsors June chapter lunch
Check back for details on the speaker and topic. Thank you to Gray Analytics for sponsoring the June 2024 NAC-ISSA chapter lunch....
EVENT FAQ
-
The March Chapter lunch is on 3/19/2019 and starts at 11:30AM
-
It is located at I3 Auditorium
-
The Address is 655 Discovery Drive, Huntsville, AL.
